This post is part of a series on contemporary best practices for promotion and tenure reviews in higher education. For a fuller picture, take a look at our recently released free best practices checklist.
Confidential evaluation letters, voting records, candidate rebuttal statements—faculty promotion and tenure cases contain highly sensitive information that must be made accessible to only the right parties during the review, and archived afterwards. But both longstanding and newer processes for managing materials can jeopardize the security of confidential information.
Here are four common ways institutions needlessly expose sensitive faculty information to the risk of access, intentionally or unintentionally, by people who aren’t supposed to view it—and how colleges and universities can guard against these risks.
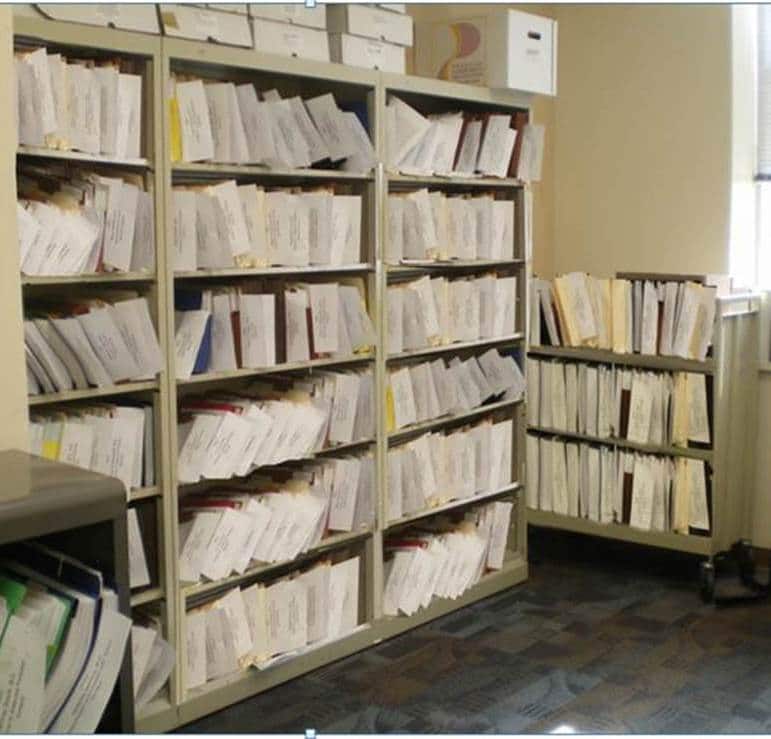
1. Paper files stored with weak physical site security
Campus rooms that are used to hold hard copies of active and archived files often have very weak security. Spaces may be left open but unmonitored when someone steps out to use the restroom or get coffee. Rooms can be accidentally left unlocked for longer periods as a result of human error or during maintenance and cleaning. And institutions often many copies of keys to locked rooms in circulation. The network of personal relationships that exist on any campus can easily give rise to situations tempting people who aren’t supposed to access materials to do so.
In addition, paper-based review processes commonly require mailing hard copies of materials to external reviewers, at which point the security of the documents are outside the institution’s control entirely.
Most campus administrative buildings just aren’t designed to be high-security environments. Rather than beefing up physical site security, it is generally more effective to adopt secure digital measures for document access and archiving, especially in light of the efficiency gains also offered by technology-based solutions.
2. Electronic copies downloaded onto travel drives or individual reviewers’ hardware
Many institutions that would never consider allowing reviewers to carry off hard copies of sensitive materials make the switch to a digital system—which turns out to allow readers (or even, amazingly, to require them) to download files of sensitive information onto their personal computers. Or—even worse—the system involves the reader walking around with confidential candidate materials on travel drives.
These processes create enormous risks. Travel drives may accidentally fall into the wrong hands. Files downloaded onto computers may remain there for years to come and be viewed by anyone who gets access to those computers either legitimately or illegitimately.
To avoid these risks, forward-thinking modern institutions increasingly seek a secure technology with in-application viewing that allows users to quickly open and read files without downloading them onto their hard drives.
3. File protections dependent on (perfect) execution of too many steps
When institutions use standard file-sharing platforms to make materials accessible to reviewers, administrative staff must manually change user access permissions multiple times for each candidate across long, complex workflows—workflows that often vary from one department or college to another. Recusals of committee members or administrators, called for due to conflict of interest, pile on further potential points of failure.
With so many different users needing differing permissions to different documents at different times along different candidates’ reviews, it becomes nearly impossible to avoid security lapses produced by human error.
This is why, in order to accomplish a safer promotion and tenure practice throughout the institution, more and more colleges and universities are searching for a system that permits automated workflows nuanced enough for all permissions and recusals to be hardwired into the review process, at the beginning of each case.
4. Digital files stored in campus servers with weak security
In higher education as in other industries, cybersecurity breaches are on the rise. Information as important as that found in P&T records merit the highest levels of security. In many cases, though, institutions store their data on servers with protection that is insufficient and outdated.
While institutions can make the continuous investments to stay ahead of illicit data access, doing so is time consuming and expensive. Most colleges and universities today recognize they get a higher level of protection, at lower cost, by using a qualified third-party partner.
Assess your school’s practices
Interested in improving the security of faculty candidate materials, or a number of other aspects of promotion and tenure review at your institution? Use this free best practices checklist to see how your processes compare to what the most progressive colleges and universities are doing.